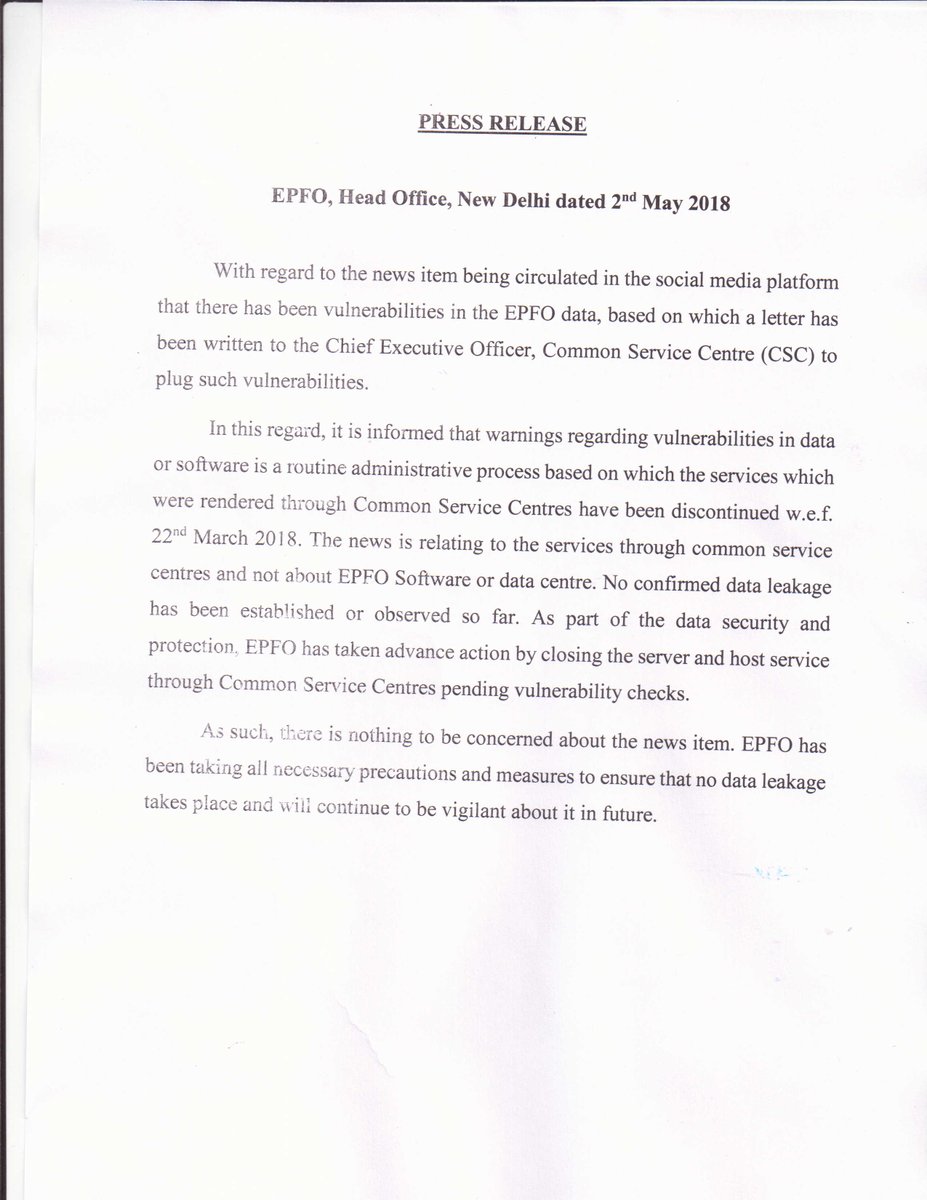
A tweet containing an image of a letter from Central Provident Fund Commissioner, Dr. V. P. Joy to CEO of theCommon Services Centre (CSC), Dinesh Tyagi appears to notify of "Data Theft from ICT Infrastructure of Aadhaar Seeding Service for Employees Provident Fund Organization" https://twitter.com/arvindgunasekar/status/991540003229454336 The letter, marked "secret" and not verified so far, references a note from the Intelligence bureau warning of theft of data by hackers by exploiting vulnerabilities on aadhaar.epfoservices.com (currently offline) - specifically, Strut vulnerability and Backdoor Shells. "The IB has advised to adhere to best practices and guidelines for securing the confidential data, re-emphasizing regular and meaningful audit and vulnerability Assessment and Penetration Testing (CAPT) of the entire System from competent auditors and testers", the letter says. The letter says that though the server is hosted at the National Data Centre, the CSC Team manages it remotely and requests the immediate deployment of an expert Technical team to identify and patch the stated vulnerabilities as well as any others on the server and notifies that the servers have been stopped and services discontinued in the interim. Earlier this year, the UIDAI had refused to renew its registrar agreement with CSC citing corruption and enrollment process violations. According to CNBC-TV18 reporting "sources", the services of CSC have been terminated after this incident. Update: The EPFO has issued a Press release saying that warnings about vulnerability are routine administrative process. "The news is regarding to the services through common service centres and not about EPFO Software…