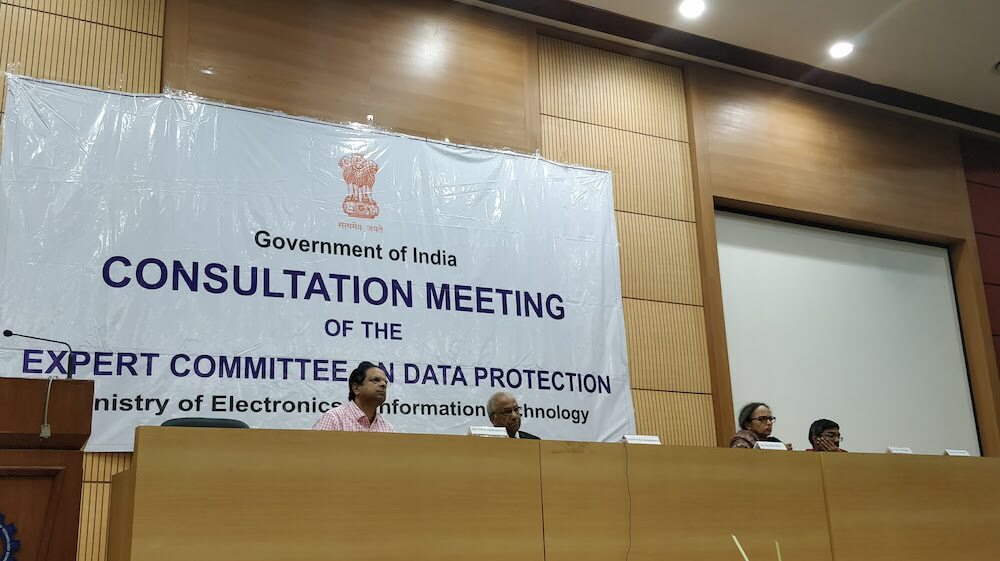
We tried to liveblog the data protection committee consultation in Mumbai yesterday, but Internet connectivity at IIT Bombay was pretty poor. Below are the comments that we were able to note down: these may somewhat paraphrased, often exact, but shouldn't be treated as a verbatim transcript. We missed some bits, and skipped some comments, which we either didn't get, or were repetitive, or when I was commenting. We've identified speakers wherever possible. Also, I reached some 15 minutes late, so only caught a part of some great opening remarks from Dr Anupam Saraph, which haven't been included below. Two fun parts: firstly, a person from Hindustan Unilever saying that he's speaking in his personal capacity, and then going on to make a company specific comment. Secondly, an ICICI Bank representative trying to justify buying personal data from clubs etc and using that for marketing (i.e. spamming). Go figure. Anyway, here are the notes from yesterday: Update: Anupam Saraph send us an email with the points he had made, which he shared with Justice Srikrishna as a letter. Here's a summary: # Is data protection technology centric? Data protection cannot be the protection of data in a particular medium like digital. We cannot create a data divide by restricting to the digital. We cannot borrow technology ideas either. For example eKYC is not KYC. KYC is not reusable as eKYC is. There is no identification in authentication. We are creating a legal mess by using authentication where identification should have happened…